Attackers see more of your brand than you do.
Phishing kits, rogue apps, leaked credentials, spoofed emails, unknown subdomains — most threats live outside your perimeter, in the internet you don't own.
TIKAJ monitors, maps and shuts down threats across your full external attack surface — automatically.
Protecting organisations across industries
The Threat Landscape
What an attacker sees when they look up your brand.
Before your security team starts their morning, attackers have already scanned your domain, crawled your subdomains, and indexed your leaked credentials. Here's what they find — and what you need to watch.
Email Identity
Your domain, weaponised against you
- Spoofed emails from your domain
- CEO / executive impersonation
- Phishing pages with your branding
- Business Email Compromise (BEC)
Brand & Web Surface
Fake versions of you, everywhere online
- Lookalike domains & clone sites
- Social media impersonation accounts
- Rogue mobile apps
- Fake customer service profiles
External Attack Surface
The digital footprint you don't know about
- Forgotten subdomains & legacy apps
- Exposed cloud storage buckets
- Leaked employee credentials
- Third-party & supply chain risk
TIKAJ exists to monitor the internet on your behalf.
We operate entirely outside your perimeter — watching the same threat infrastructure attackers use — so your team sees threats that internal security tools simply can't reach.
Prevent · Detect · Respond
One platform. Every threat vector.
From phishing simulations to compliance automation — TIKAJ handles the full security lifecycle so your team doesn't have to.
Stop the #1 breach vector before it hits your org.
Most breaches start with a human click. PhishGrid runs live phishing simulations so employees learn from realistic attacks — before a real attacker gets the chance.
- Launch tailored phishing simulations across your org
- Educate teams with real-time learning after clicks
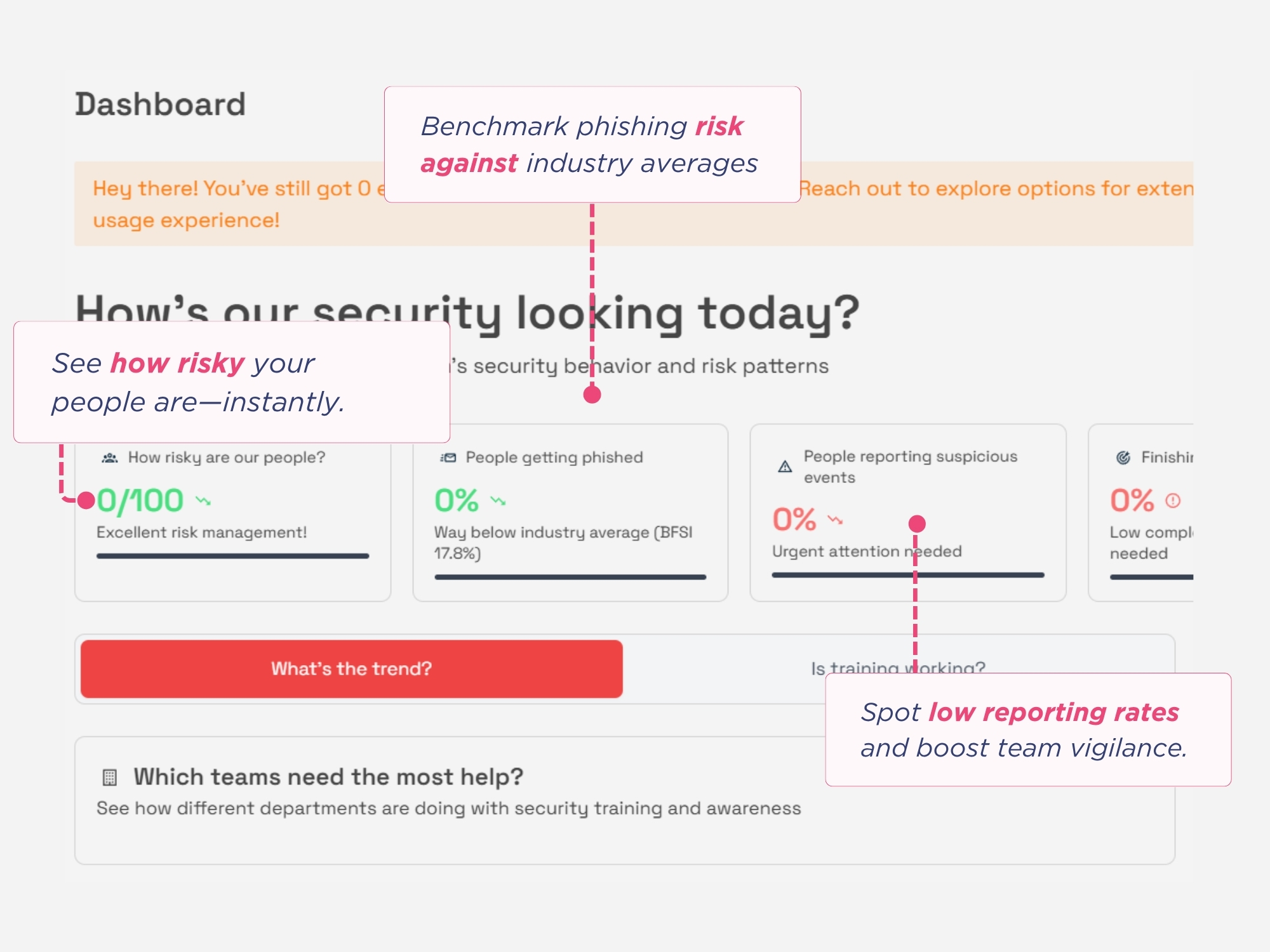
- Track awareness trends with smart dashboards
The Security Lifecycle
One platform. Every stage of defence.
Security isn't a product. It's a continuous cycle of prevention, detection and response — with compliance woven through every stage. TIKAJ covers it all.
01
Prevent
Harden before attackers probe.
Most breaches are preventable. TIKAJ identifies your exposed assets, locks down email authentication with DMARC, and trains employees with live phishing simulations — collapsing the attack surface before threats arrive.
Learn how we handle thisWhat TIKAJ delivers
- Email domain lockdown (DMARC/SPF/DKIM)
- External Attack Surface Mapping
- Employee phishing simulation & training
- Threat-informed security advisories
Trusted by Companies Worldwide
We serve cybersecurity needs across borders in over 5 countries and industries ranging from fintech to telecom.
100+
customers across 10+ industries
Trusted. Proven. Scalable.
Top 3
e-commerce company in India
Securing daily commerce.
Top 10 global
telecom provider
Powering safe connectivity.
Integrations
Works with your existing stack
TIKAJ seamlessly integrates with 100+ popular platforms — SIEMs, ticketing systems, communication apps, cloud providers, and more.
Explore our integrationsWhat Our Clients Say
Trusted by Security Leaders
Hear from CISOs and IT leaders who rely on TIKAJ to protect their organisations.
"Highly satisfied with TIKAJ's flawless service and quick response. I recommend their products and services for their consistent efficiency and customer satisfaction. A pleasure to be associated with them!"

CISO, E-commerce
35Bn
"TIKAJ impresses with a user-friendly approach and tailored solutions. Seamless experience, no room for improvement. Discovered them on their website, highly recommend their products and services. Keep up the good work!"

Head of IT, Fintech
"Satisfied with TIKAJ's smooth services, especially their impressive takedown process. I'd recommend them for repost opportunities and reliable DMARC service."

CISO, Fintech
30mn USD
FAQ
Frequently Asked Questions
Trusted by 100+ clients and partners
Ready to get protected?
See your external attack surface — before an attacker does.
Get a live demo tailored to your industry. No commitment, no setup required.