
7 Things You Must Know About Email Security!
Your inbox is possibly at the focal point of your work life. Email functions as a communication tool for enterprises. Nonetheless, it’s […]

Your inbox is possibly at the focal point of your work life. Email functions as a communication tool for enterprises. Nonetheless, it’s […]
The LockBit ransomware-as-a-service (RaaS) gang has ramped up its targeted attacks, researchers said, with attempts against organizations in Chile, Italy, Taiwa
Regardless of whether it’s ransomware, the supply chain, or another detestable technique, cyber actors how to recognize the organization’s shaky areas, which, [

Here is a fun guide for you to keep your mobile phones protected always, in all ways!

As Cybersecurity Awareness Month has started already, we invite you to check our awareness special Infographic for this week.
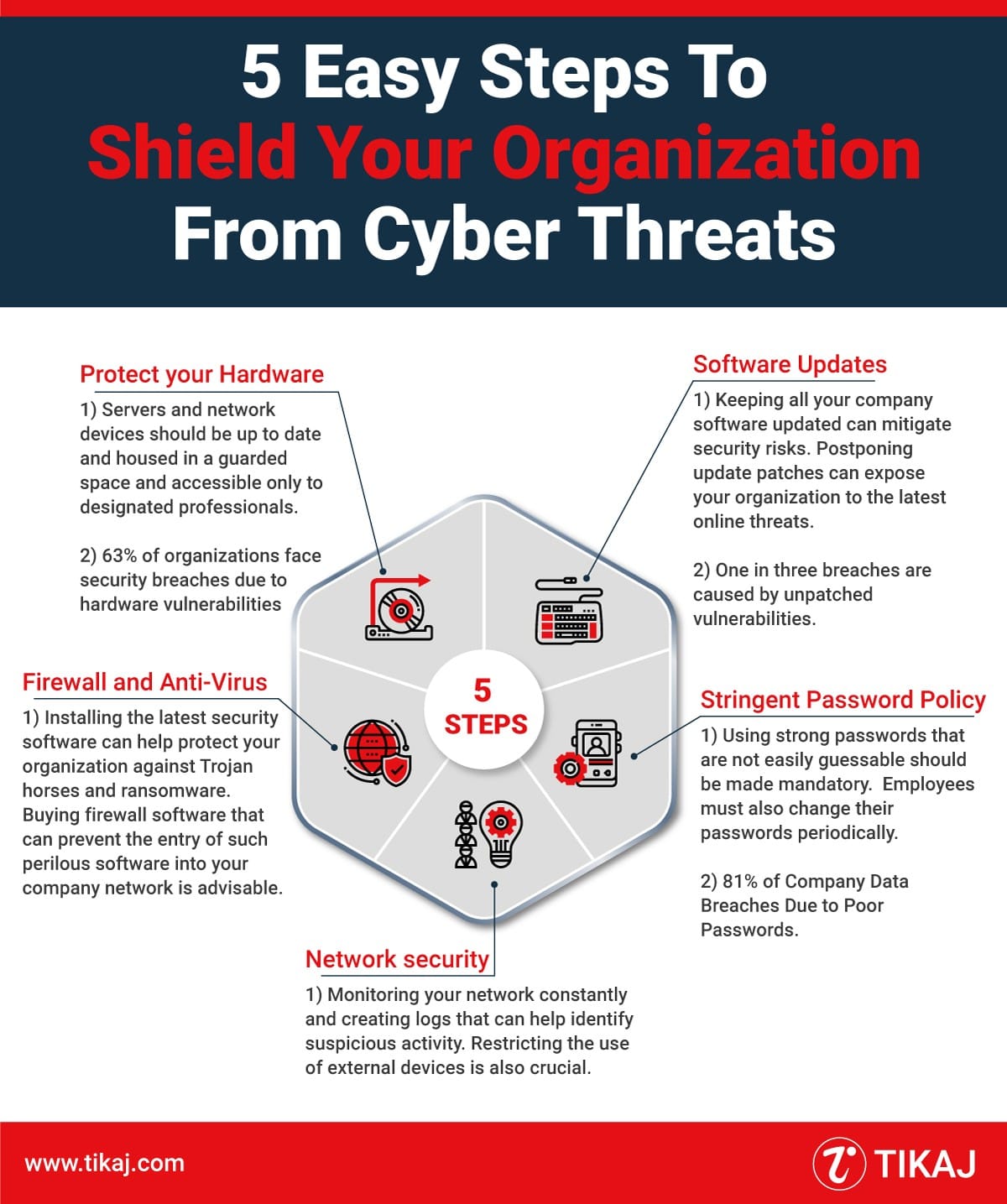
Infographic illustrating Easy steps to shield your organisation from cyber threats
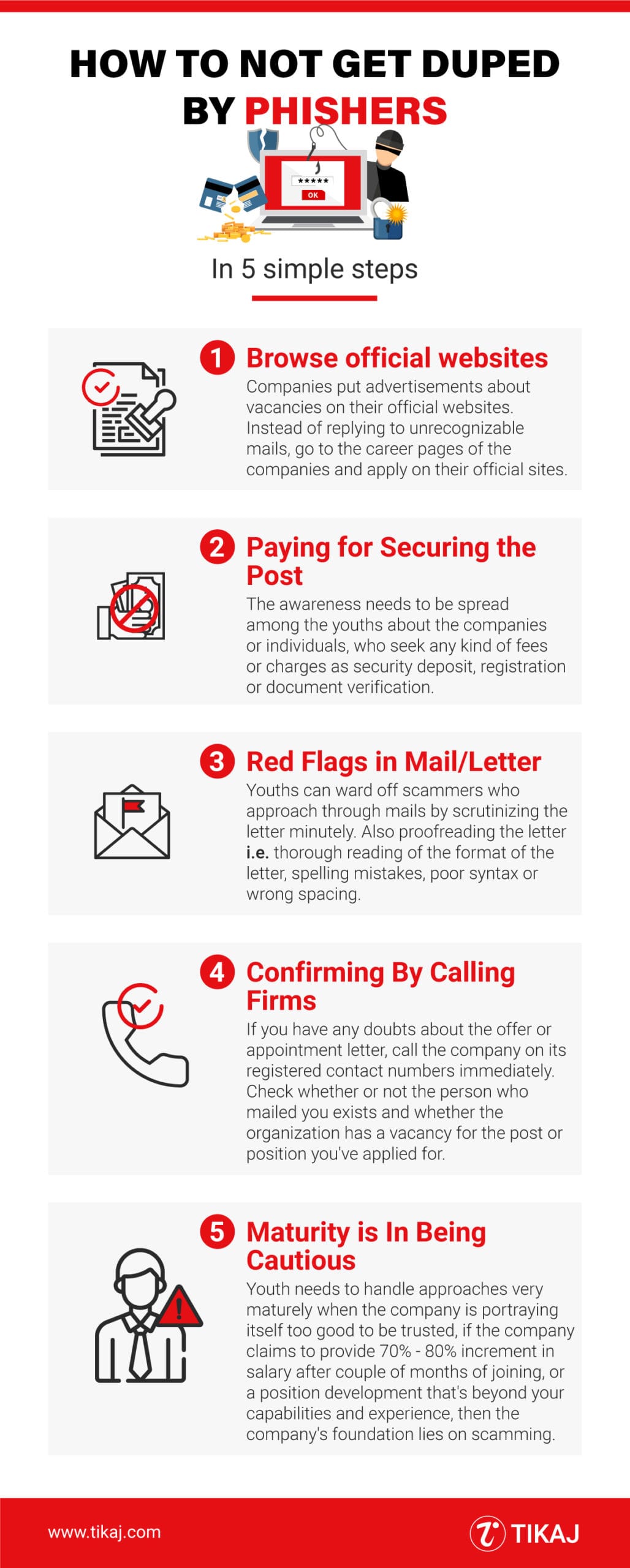
Learn how to protect yourself from phishing scams with these 5 easy steps. Don’t fall victim to phishers – follow our expert […]
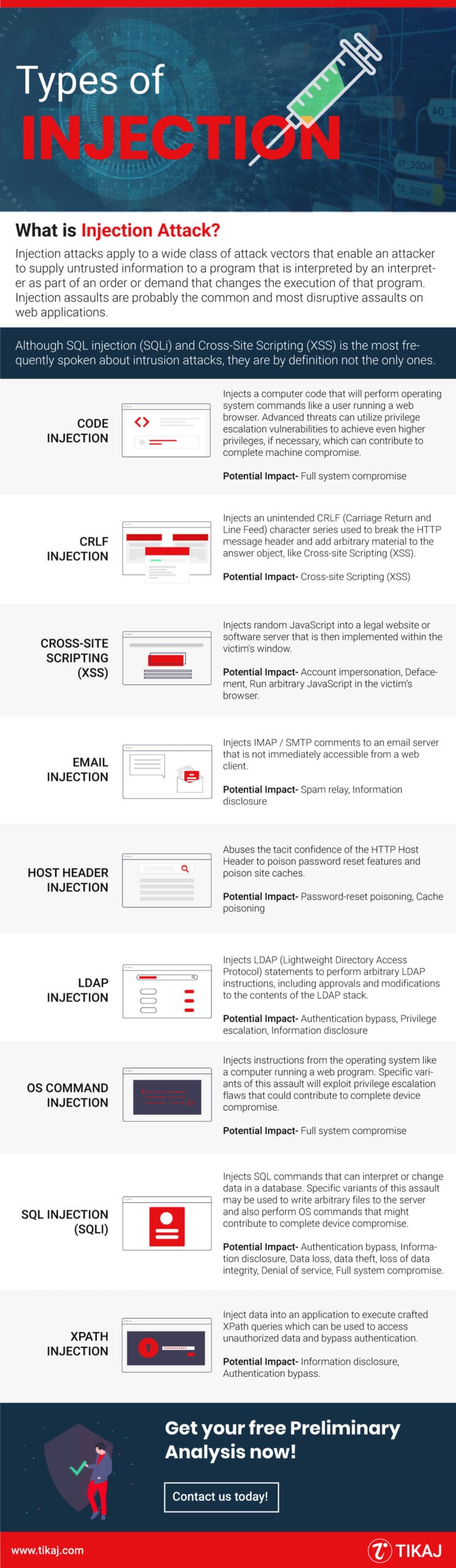
What is an Injection Attack? Injection attacks apply to a wide class of attack vectors that enable an attacker to supply untrusted […]
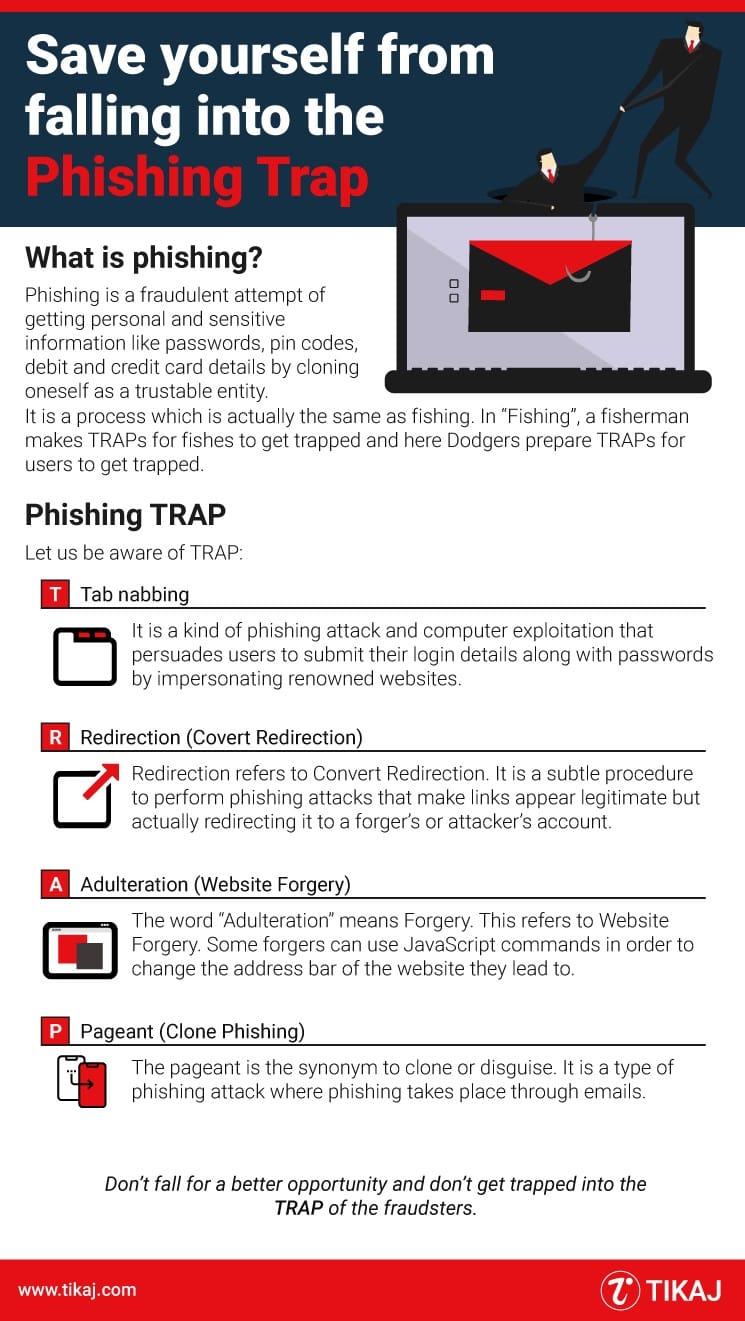
What is Phishing? Phishing is a fraudulent attempt of getting personal and sensitive information like passwords, pin codes, debit, and credit card […]

What is SIEM? Security information and Event Management (SIEM) is a combination of System Information Management (SIM) and System Event Management (SEM) [&helli