DKIM Simplified
DomainKeys Identified Mail (DKIM), is a mechanism that allows verification of the source and contents of email messages. Using DKIM, sending domains […]
Expert insights on cybersecurity, threat intelligence, email protection, and digital risk management.
DomainKeys Identified Mail (DKIM), is a mechanism that allows verification of the source and contents of email messages. Using DKIM, sending domains […]

Did you mask your network as well during COVID-19? COVID-19 continues to significantly embolden cybercriminals’ phishing and fraud efforts, and there is [&helli
Sender Policy Framework (SPF) is an email validation system designed to detect and block forged or spoofed emails. This is done by verifying […]

Keylogging (also called keystroke logging) is a method that cyber criminals use to record (or log) the keys you strike on your […]
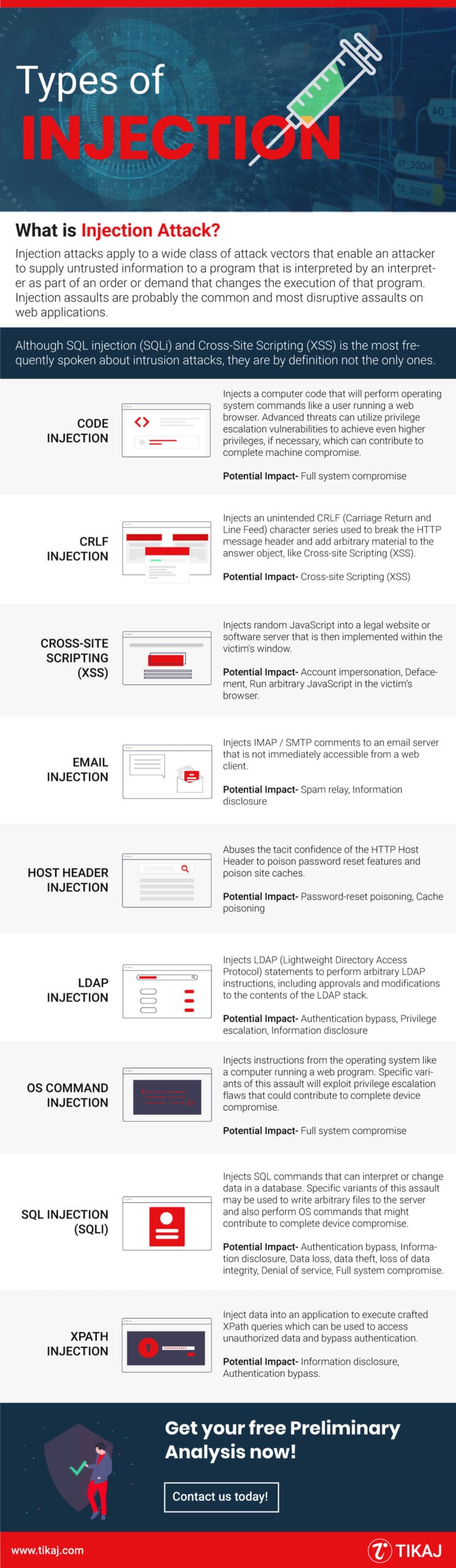
What is an Injection Attack? Injection attacks apply to a wide class of attack vectors that enable an attacker to supply untrusted […]
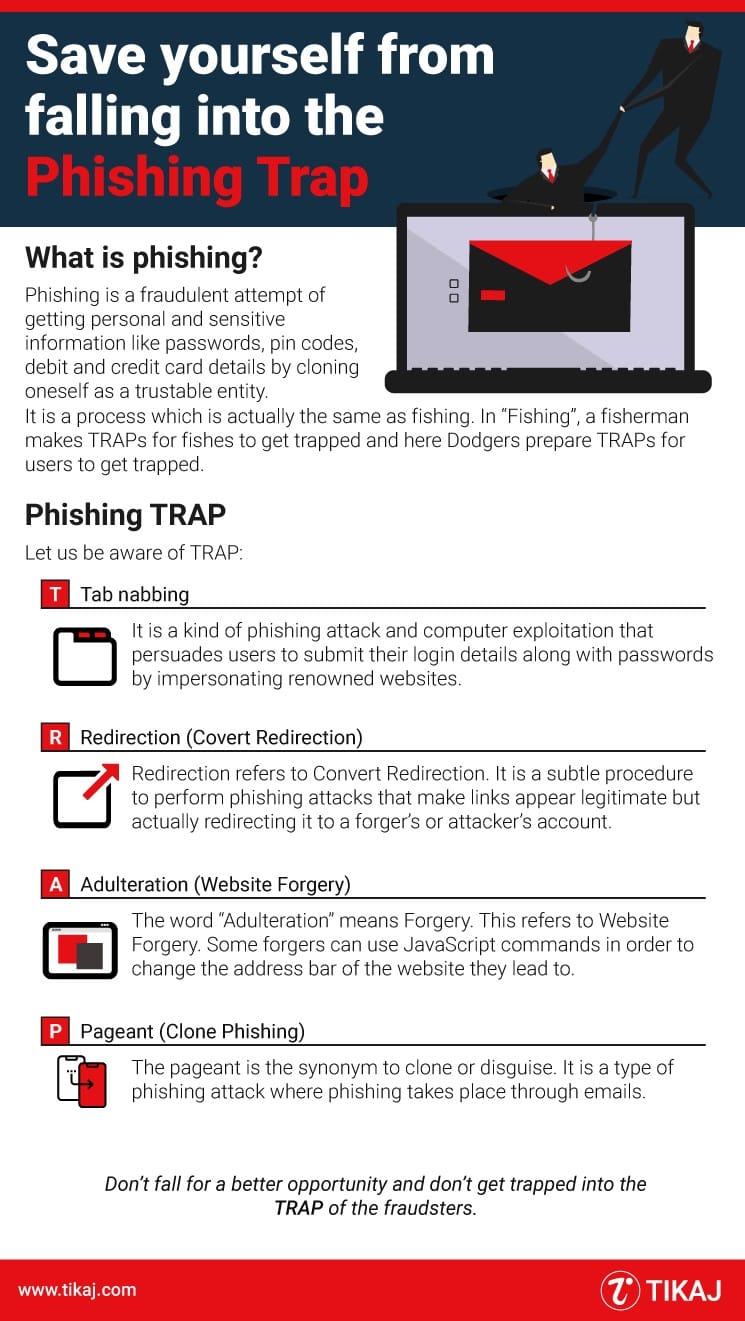
What is Phishing? Phishing is a fraudulent attempt of getting personal and sensitive information like passwords, pin codes, debit, and credit card […]